Leave your worries behind, knowing your business is always being looked after. Our highly qualified, professional dispatchers handle your account up to Safe and Sound’s high standards of service at all times. In addition to intrusion, we monitor life-safety and environmental conditions. We can supervise the open and close activity of your alarm system. We will call, text or e-mail when your system is not armed on time, and provide you with reports for your permanent records. We can personalize your account activity notification for your convenience and to meet your specific business needs. We have the utmost consideration for your confidential records and information. With multiple monitoring center locations in different parts of the country, You’re covered regardless of what happens. Rest assured that we will take care of your business as if it were our own.
Monitoring Services
Our highly trained, professional staff monitor activity at your business 24 hours a day, 7 days a week, 365 days a year. We have the most up-to-date, state-of-the-art equipment and communications network to receive signals directly from your alarm system. With multiple monitoring centers all over the country, you can rest assured that your home or business will be monitored no matter what might occur. We focus on multiple communication methods for your system to talk to the main monitoring station and always use cellular communication for maximum reliability. Our Monitoring Center Team provides a reliable and quick precision response for your safety and protection needs. Call us today to take over your existing system, or get all new equipment, most of which is normally free with new contract terms.
- Burglar intrusion alarm
- Water/flood detection
- Hold up, panic, ambush
- Perimeter detection
- Supervision of open/close activity with reports
- Carbon Monoxide detection
- Hi-Low Temperature detection (for heat or cold)
- Power and Low battery supervision
Camera Systems
Safe and Sound is dedicated to providing a handcrafted, specifically tailored surveillance system for each and every one of our clients. We will present multiple solutions every time. We understand that there are hundreds of surveillance product companies, methods of install, and placement options for every new project we take on. Our standard practice is to show three options on every project, and we will make countless revisions to dial in the system to specifically what is needed by our clients. Above all, we are fairly priced, easy to work with, and highly effective at what we do.
CCTV Beginnings
The first CCTV system was installed by Siemens AG at Test Stand VII in Peenemünde, Germany in 1942, for observing the launch of V-2 rockets. The noted German engineer Walter Bruch was responsible for the technological design and installation of the system.
A Brief History of IP Cameras
The first centralized IP camera was released in 1996 by Axis Communications. It was called the Axis Neteye 200 and was developed by the team of Martin Gren and Carl-Axel Alm. It used a custom web server internal to the camera. In late 1999, the company started using embedded Linux to operate its cameras. Axis also released documentation for its low-level API called “VAPIX”, which builds on the open standards of HTTP and real time streaming protocol (RTSP). This open architecture was intended to encourage third-party software manufacturers to develop compatible management and recording software.
IP Camera Standards
Analog closed circuit television uses established broadcast television formats (e.g. Common Intermediate Format (CIF), NTSC, PAL, and SECAM). Generally speaking, each make of IP camera will differ in its features and functions, video encoding (compression) schemes, available network protocols, and the API to be used by video management software.
In order to address issues of standardization of IP video surveillance, two industry groups were formed in 2008: the Open Network Video Interface Forum (ONVIF) and the Physical Security Interoperability Alliance (PSIA). While the PSIA was founded by 20 member companies including Honeywell, GE Security and Cisco, and ONVIF was founded by Axis Communications, Bosch and Sony, each group now has numerous members. As of January 2009, each group had released version 1.0 of their specification.
Potential advantages of IP Cameras
- Two-way audio via a single network cable allows users to communicate with what they are seeing (e.g. gas station clerk assisting a customer on how to use the prepay pumps)
- Flexibility: IP cameras can be moved around anywhere on an IP network (including wireless).
- Distributed intelligence: with IP cameras, video analytic’s can be placed in the camera itself allowing scale-able analytic’s solutions.
- Transmission of commands for PTZ (pan, tilt, zoom) cameras via a single network cable.
- Encryption & authentication: IP cameras offer secure data transmission through encryption and authentication methods such as WEP, WPA, WPA2, TKIP, AES.
- Remote accessibility: live video from selected cameras can be viewed from any computer, anywhere, and also from many mobile smartphones and other devices.
- IP cameras are able to function on a wireless network.
- PoE – Power over Ethernet: Modern IP cameras have the ability to operate without an additional power supply. They can work with the PoE-protocol which gives power via the Ethernet cable.
Potential disadvantages of IP Cameras
- High network bandwidth requirements
- As with a CCTV/DVR system, if the video is transmitted over the public Internet rather than a private IP LAN, the system becomes open to a wider audience of hackers and hoaxers. Criminals can hack into a CCTV system to observe security measures and personnel, thereby facilitating criminal acts and rendering the surveillance counterproductive.
Distributed Audio Sound Systems
We have a full portfolio of pro audio and commercial audio equipment. Our team has completed sound systems for elementary schools, high schools, retail locations, and even clubs and movie theaters.
Computers and Networking
We offer a full range of computer and networking services. Below is our list:
Point of Sale setup and maintenance
Computer diagnostics
Computer repair
Network setup
Network monitoring and security
WiFi setup and security
Virus removal
Hardware upgrades
Software upgrades
Access Control
The term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons. Physical access control can be achieved through technological means such as access control systems. Safe and Sound is the team of professionals you need to help you chose the right product for your application. We constantly explore more innovative and cost-effective solutions to provide the best solutions.
Physical access control is a matter of who, where, and when. An access control system determines who is allowed to enter or exit, where they are allowed to exit or enter, and when they are allowed to enter or exit. Historically, this was partially accomplished through keys and locks. When a door is locked, only someone with a key can enter through the door, depending on how the lock is configured. Mechanical locks and keys do not allow restriction of the key holder to specific times or dates. Mechanical locks and keys do not provide records of the key used on any specific door, and the keys can be easily copied or transferred to an unauthorized person. When a mechanical key is lost or the key holder is no longer authorized to use the protected area, the locks must be re-keyed. The cost of personnel changes are greatly increased.
Electronic access control uses computer boards to solve the limitations of mechanical locks and keys. A wide range of credentials can be used to replace mechanical keys. The electronic access control system grants access based on the credential presented. When access is granted, the door is unlocked for a predetermined time and the transaction is recorded. When access is refused, the door remains locked and the attempted access is recorded. The system will also monitor the door and alarm if the door is forced open or held open too long after being unlocked.
Access control system operation
When a credential is presented to a reader, the reader sends the credential’s information, usually a number, to a control panel, a highly reliable processor. The control panel compares the credential’s number to an access control list, grants or denies the presented request, and sends a transaction log to a database. When access is denied based on the access control list, the door remains locked. If there is a match between the credential and the access control list, the control panel operates a relay that in turn unlocks the door. The control panel also ignores a door open signal to prevent an alarm. Often the reader provides feedback, such as a flashing red LED for an access denied and a flashing green LED for an access granted.
The above description illustrates a single factor transaction. Credentials can be passed around, thus subverting the access control list. For example, Alice has access rights to the server room, but Bob does not. Alice either gives Bob her credential, or Bob takes it; he now has access to the server room. To prevent this, two-factor authentication can be used. In a two factor transaction, the presented credential and a second factor are needed for access to be granted; another factor can be a PIN, a second credential, operator intervention, or a biometric input.
There are three types (factors) of authenticating information:
- something the user knows, e.g. a password, pass-phrase or PIN
- something the user has, such as smart card or a key fob
- something the user is, such as fingerprint, verified by biometric measurement
Passwords are a common means of verifying a user’s identity before access is given to information systems. In addition, the fourth factor of authentication is now recognized: someone you know, whereby another person who knows you can provide a human element of authentication in situations where systems have been set up to allow for such scenarios. For example, a user may have their password but have forgotten their smart card. In such a scenario, if the user is known to designated cohorts, the cohorts may provide their smart card and password, in combination with the extant factor of the user in question, and thus provide two factors for the user with the missing credential, giving three factors overall to allow access.
Credential’s
A credential is a physical/tangible object, a piece of knowledge, or a facet of a person’s physical being, that enables an individual access to a given physical facility or computer-based information system. Typically, credentials can be something you know (such as number or PIN), something you have (such as an access badge), something you are (such as a biometric feature) or some combination of these items. The typical credential is an access card, key-fob, or other keys. There are many card technologies including magnetic stripe, bar code, Wiegand, 125 kHz proximity, 26-bit card-swipe, contact smart cards, and contactless smart cards. Also available are key-fobs, which are more compact than ID cards, and attach to a key ring. Typical biometric technologies include fingerprint, facial recognition, iris recognition, retinal scan, voice, and hand geometry.
Access control system components
An access control point, which can be a door, turnstile, parking gate, elevator, or other physical barriers, where granting access can be electronically controlled. Typically, the access point is a door. An electronic access control door can contain several elements. At its most basic, there is a stand-alone electric lock. The lock is unlocked by an operator with a switch. To automate this, operator intervention is replaced by a reader. The reader could be a keypad where a code is entered, it could be a card reader, or it could be a biometric reader. Readers do not usually make an access decision, but send a card number to an access control panel that verifies the number against an access list. To monitor the door position a magnetic door switch can be used. In concept, the door switch is not unlike those on refrigerators or car doors. Generally, only entry is controlled, and exit is uncontrolled. In cases where the exit is also controlled, a second reader is used on the opposite side of the door. In cases where the exit is not controlled, free exit, a device called a request-to-exit (REX) is used. Request-to-exit devices can be a push-button or a motion detector. When the button is pushed, or the motion detector detects motion at the door, the door alarm is temporarily ignored while the door is opened. Exiting a door without having to electrically unlock the door is called mechanical free egress. This is an important safety feature. In cases where the lock must be electrically unlocked on exit, the request-to-exit device also unlocks the door.

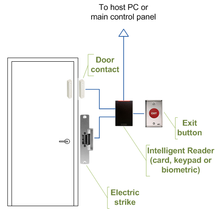
Typical access control door wiring
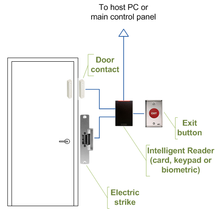
Access control door wiring when using intelligent readers
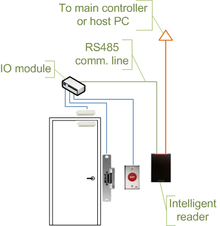
Access control door wiring when using intelligent readers and IO module

Typical access control door wiring
Call or write with questions:
info@ineedatek.com
(855)-SAFE-900
NO initial consulting FEE!
*(within our local service area, ask for details)
